Resource Library
Brochures | White Papers | Datasheets
(Bookmark this page or visit www.techr2.com/library for future access)
| Preview | Title | File Type | File Size | hf:doc_categories | |
|---|---|---|---|---|---|
| 110 TechR2 | Tear A Byte® TRIFOLD BRO | 11 MB | brochures | |||
| 112 TechR2 | About TechR2 | 1 MB | brochures | |||
| 115 TechR2 | Tear A Byte® | 2 MB | brochures | |||
| 125 TechR2 | SMART TechBOX | 2 MB | brochures | |||
| 137 TechR2 | Tear A Byte® 24U | 1 MB | brochures | |||
| 138 TechR2 | Tear A Byte® 24U Datasheet | 2 MB | datasheets | |||
| 139 TechR2 | Tear A Byte® 42U Datasheet | 2 MB | datasheets | |||
| 140 TechR2 | Tear A Byte® 10U Datasheet | 2 MB | datasheets | |||
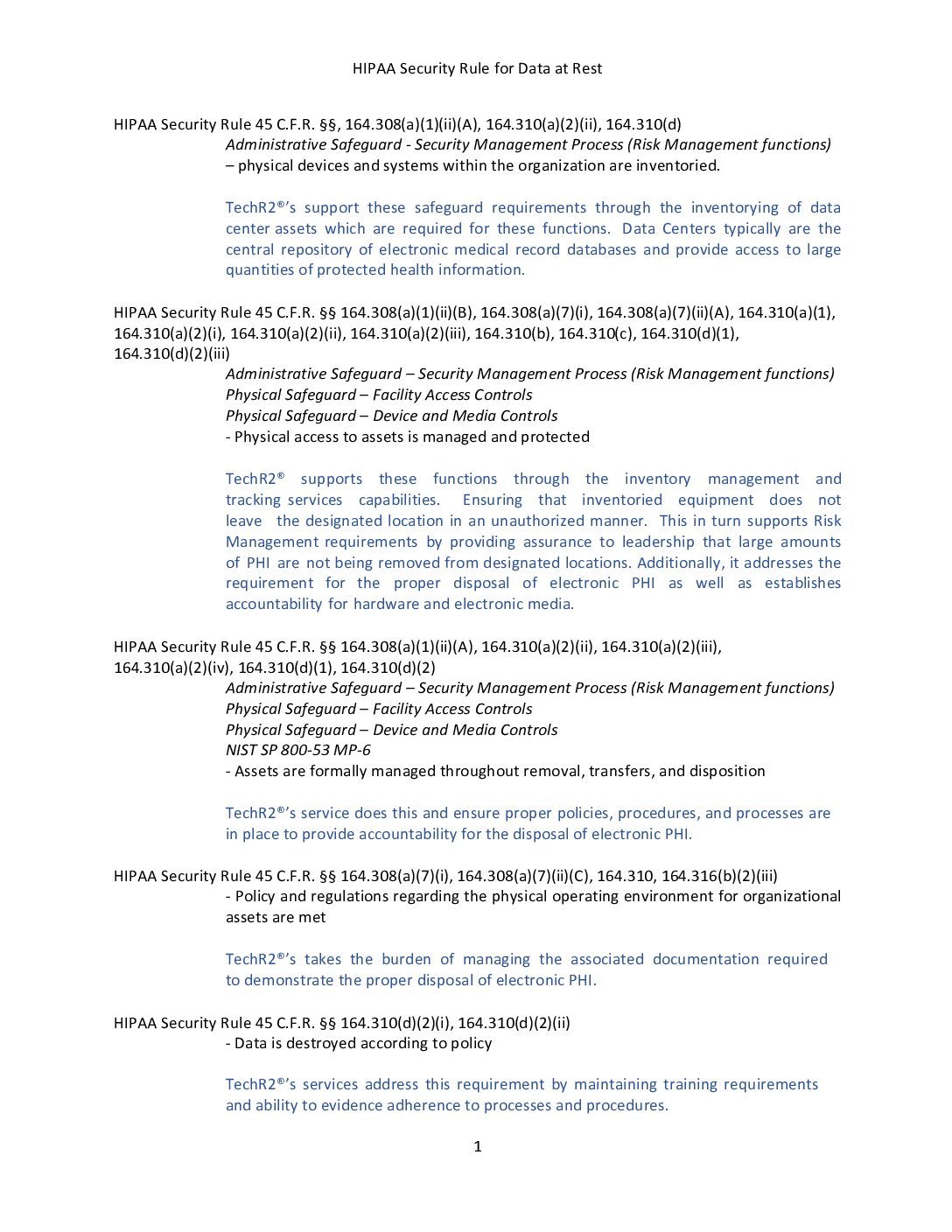
| 148 TechR2 | Health Industry Regulations | 205 KB | white-papers | |||
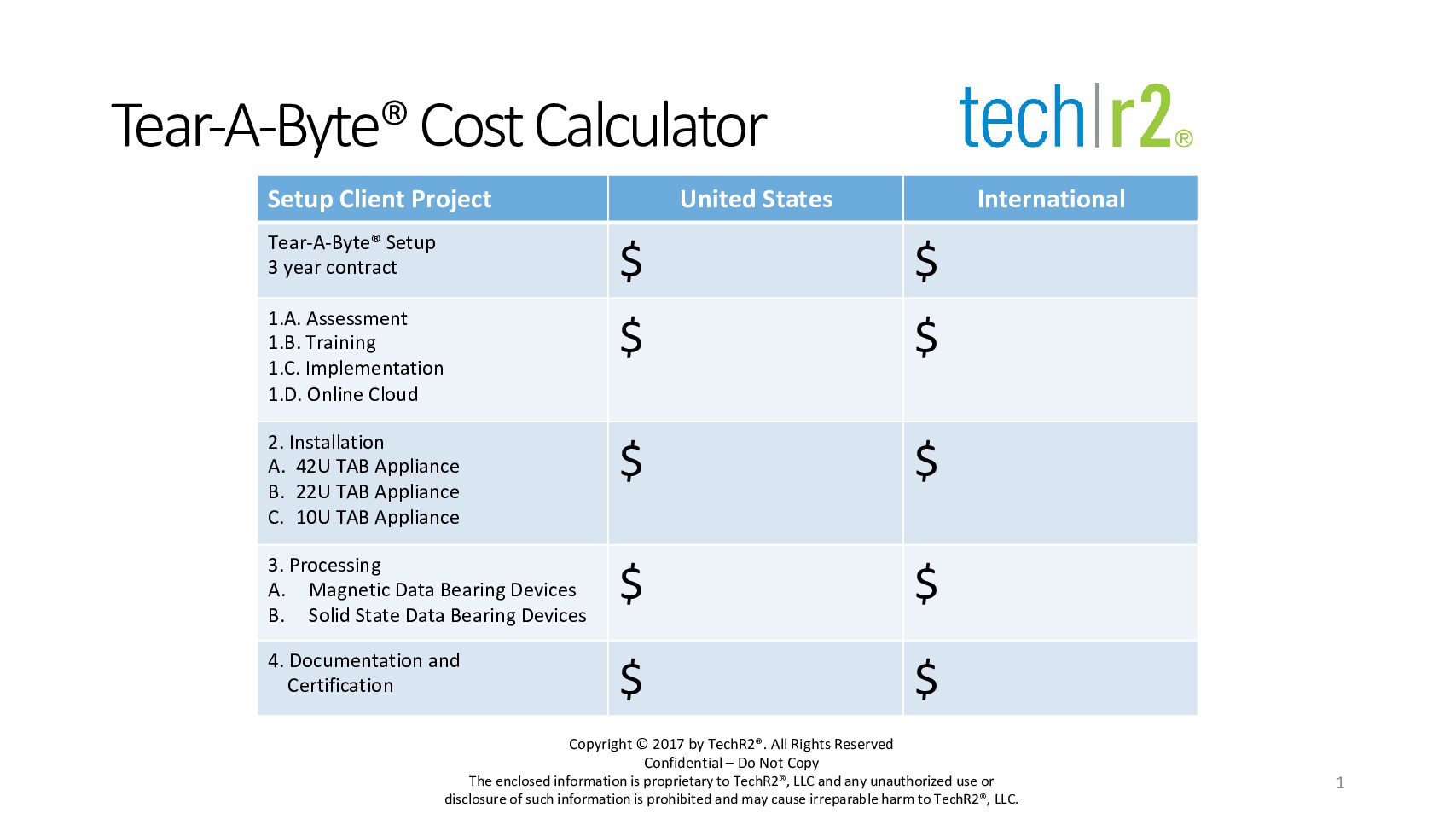
| 150 TechR2 | Tear A Byte® Cost Calculator | 112 KB | white-papers | |||
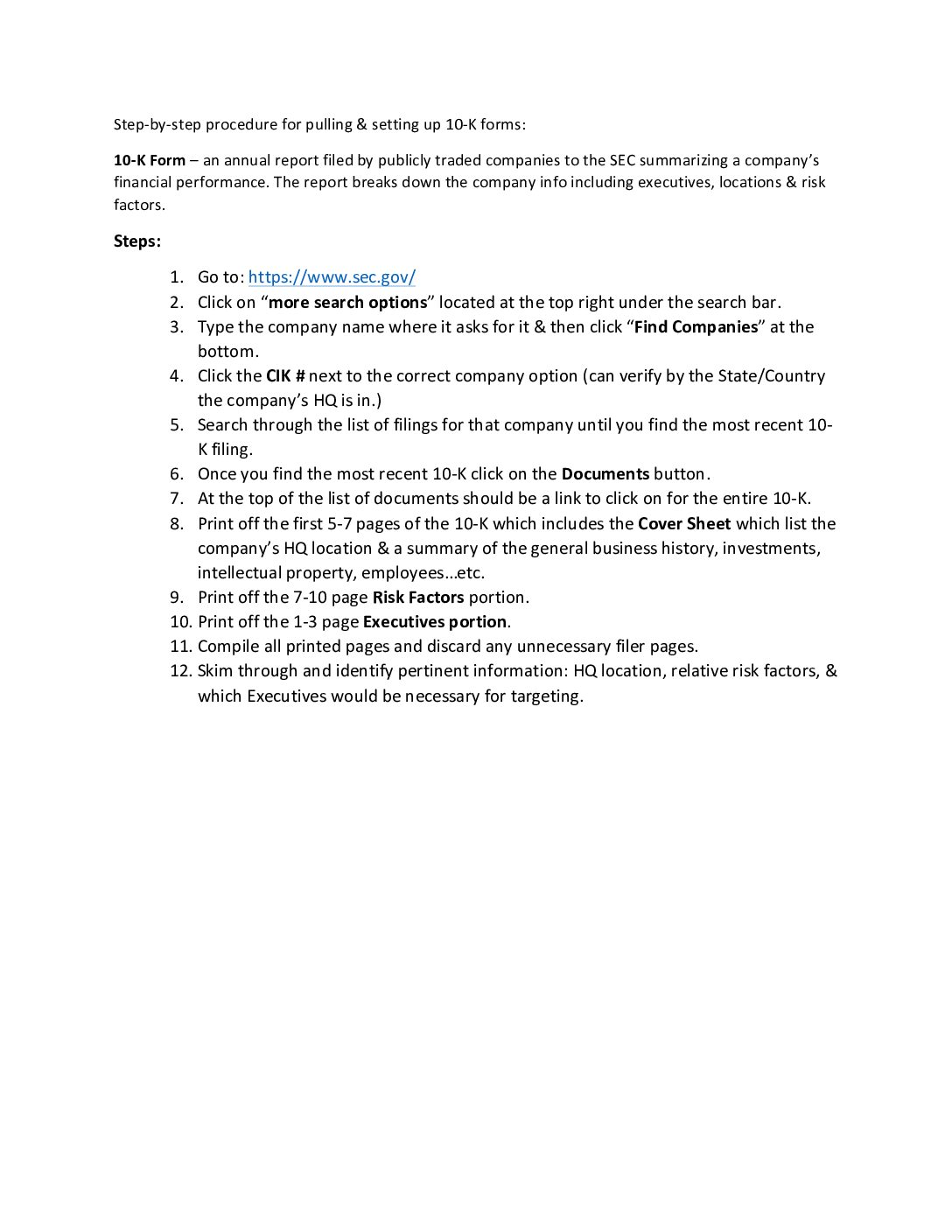
| 151 TechR2 | 10 K Procedure | 48 KB | white-papers | |||
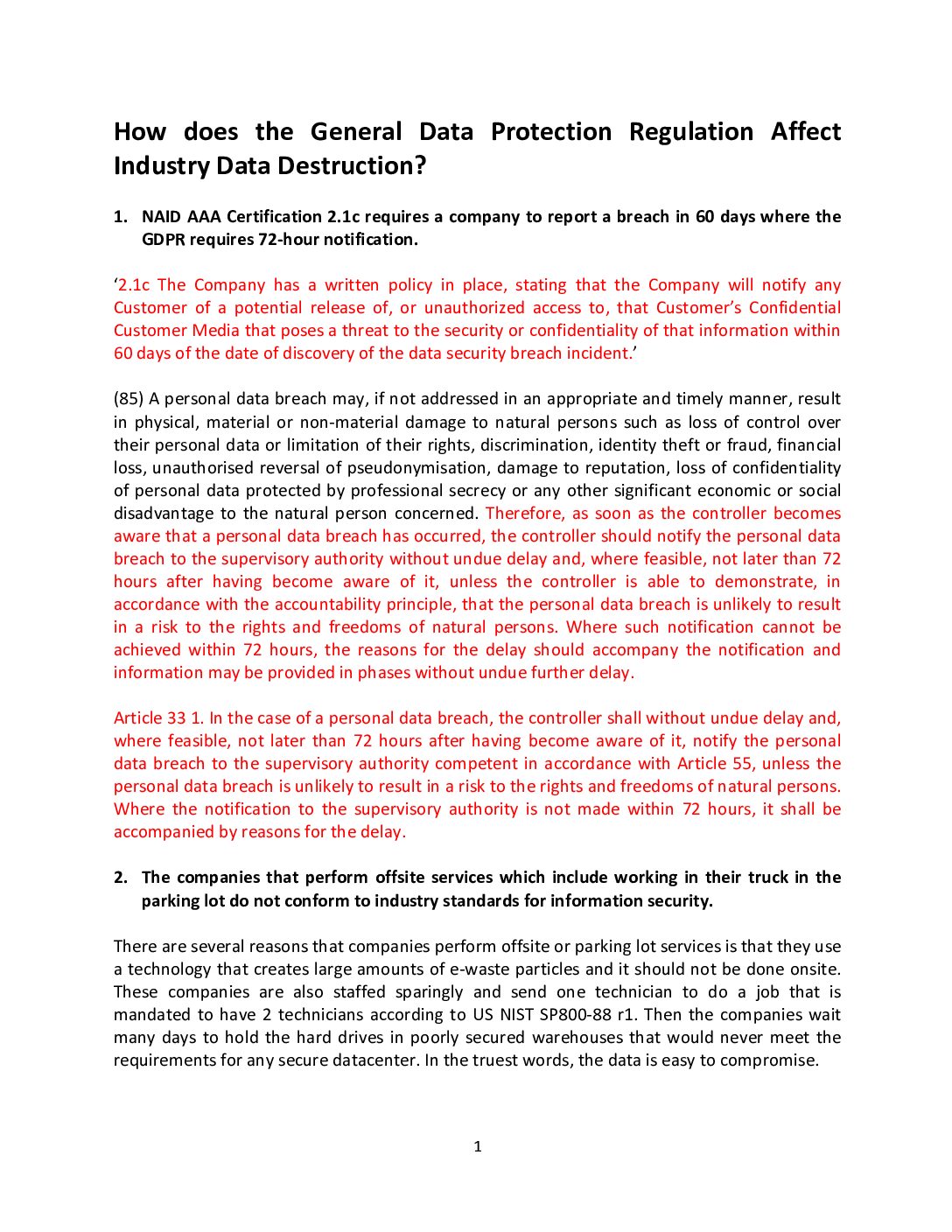
| 152 TechR2 | How GDPR Affects Data Destruction | 83 KB | white-papers | |||
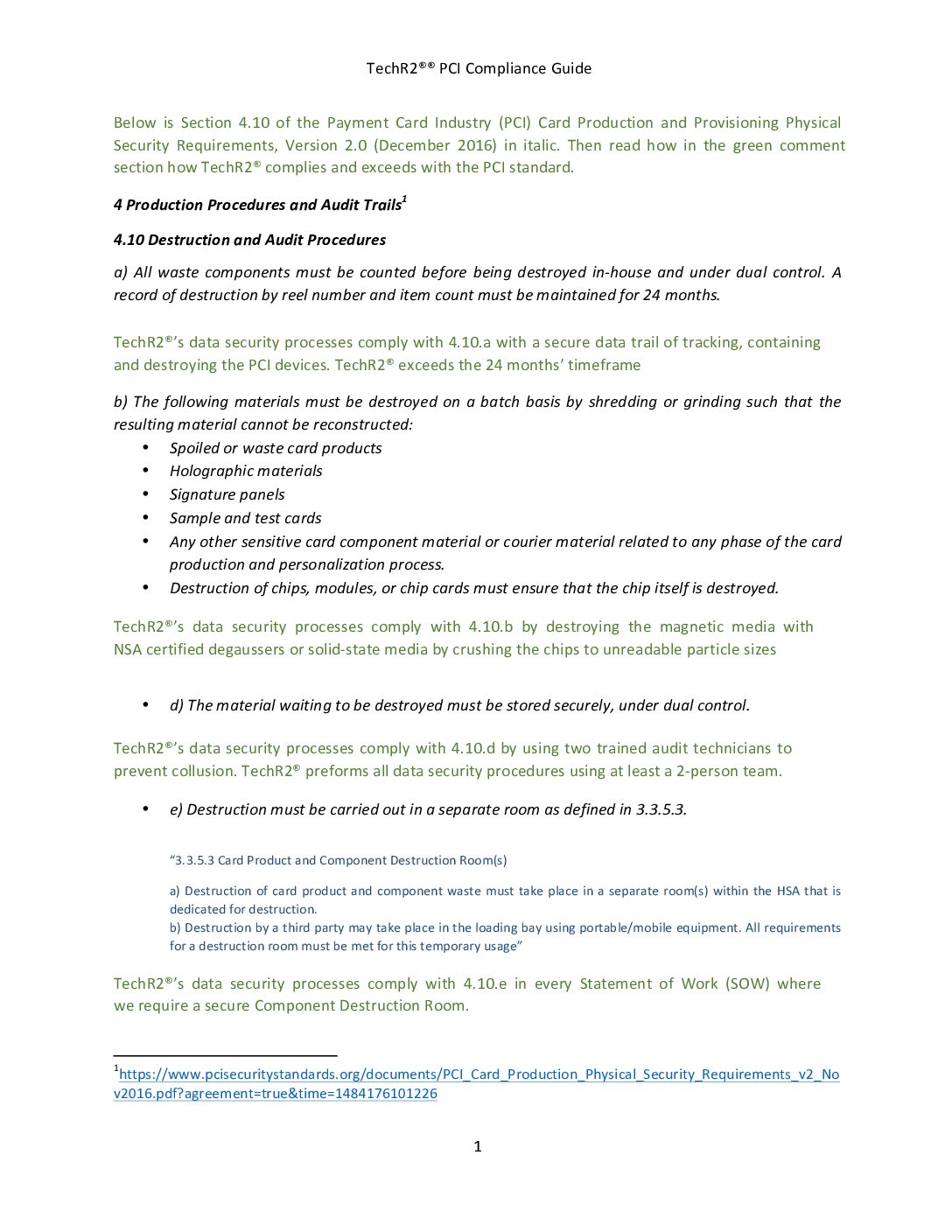
| 153 TechR2 | PCI Compliance Guide | 563 KB | white-papers | |||
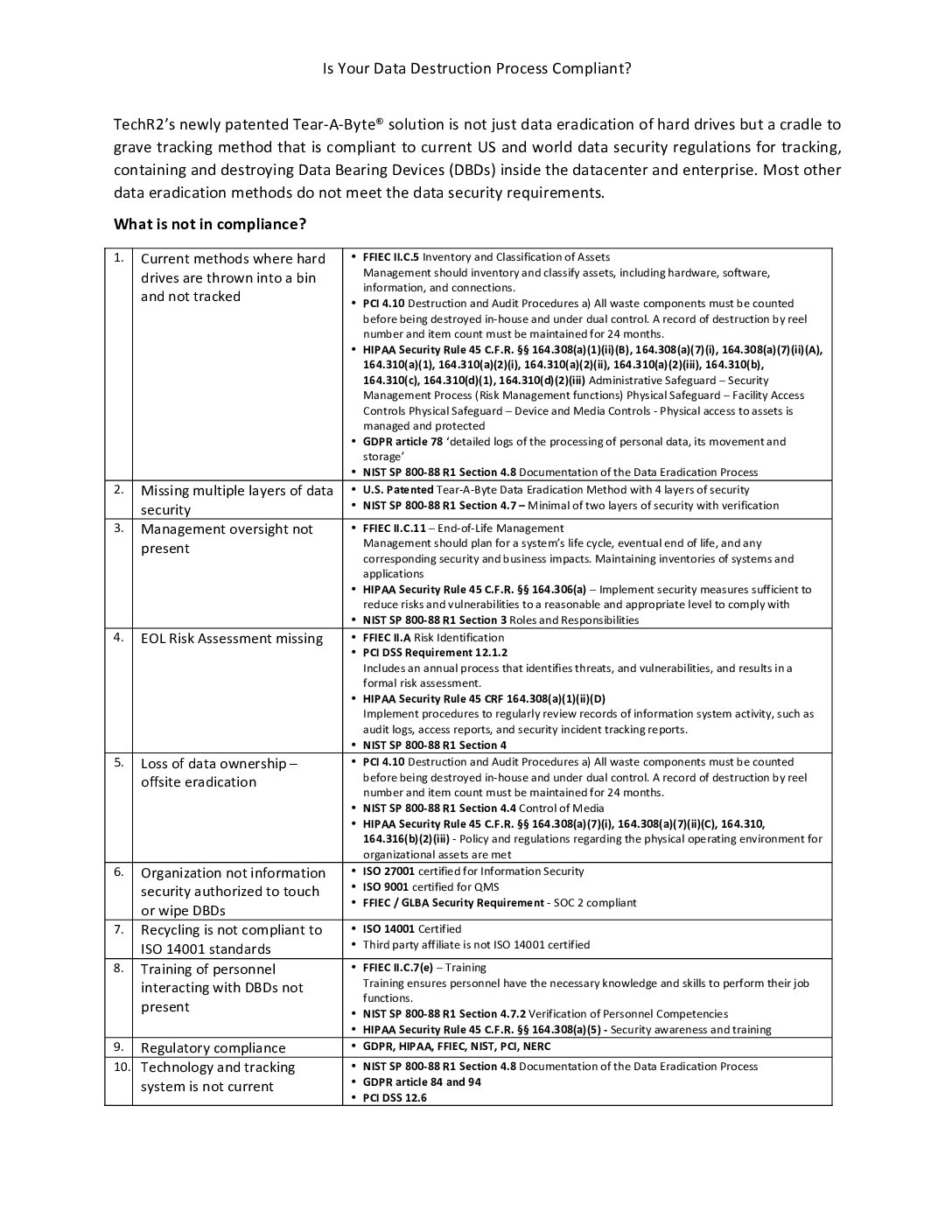
| 154 TeachR2 | Is Your Data Destruction Process Compliant | 64 KB | white-papers | |||
| 156 TechR2 | Overcoming Objections | 404 KB | white-papers | |||
| 157 TechR2 | Plan by Industry | 66 KB | white-papers | |||
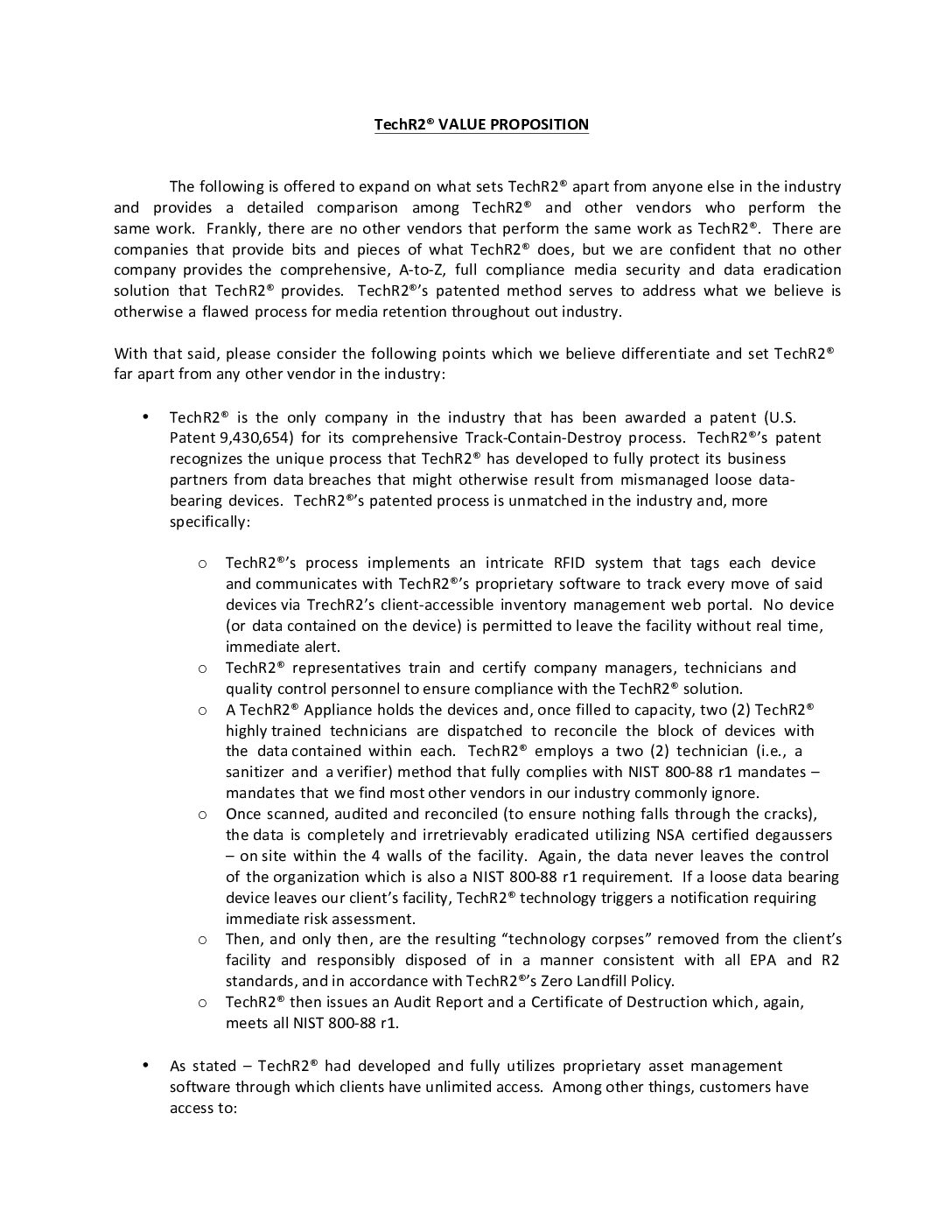
| 158 TechR2 | Value Proposition | 816 KB | white-papers | |||
| 167 TechR2 | Security Weaknesses | 2 MB | white-papers | |||
| 171 TechR2 | Cleanout | 2 MB | white-papers | |||
| 174 TechR2 | Data Tape Destruction | 2 MB | white-papers | |||
| 176 TechR2 | Achieving Compliance – Data Storage Security | 3 MB | white-papers | |||
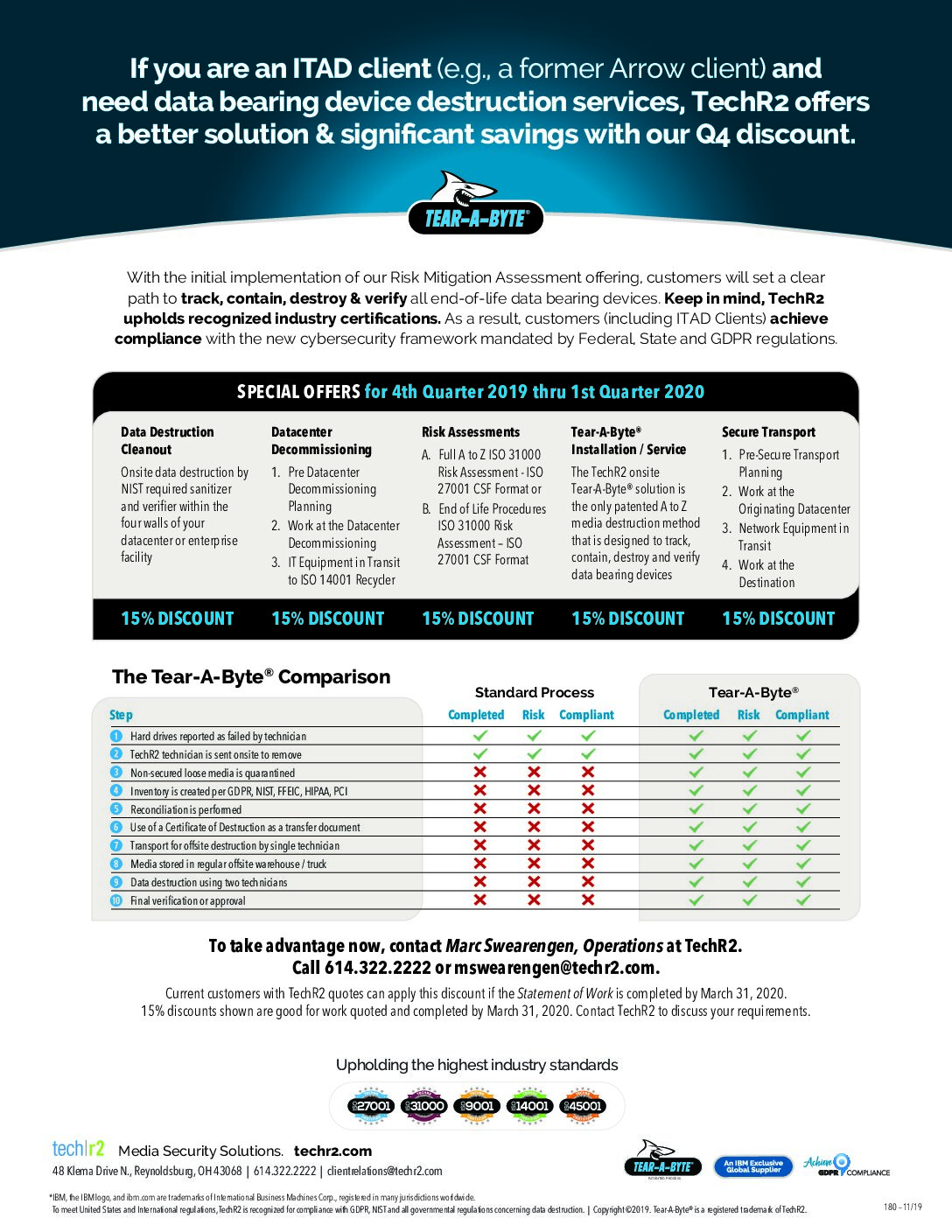
| 180 TechR2 | 4Q 25 | 2 MB | white-papers | |||
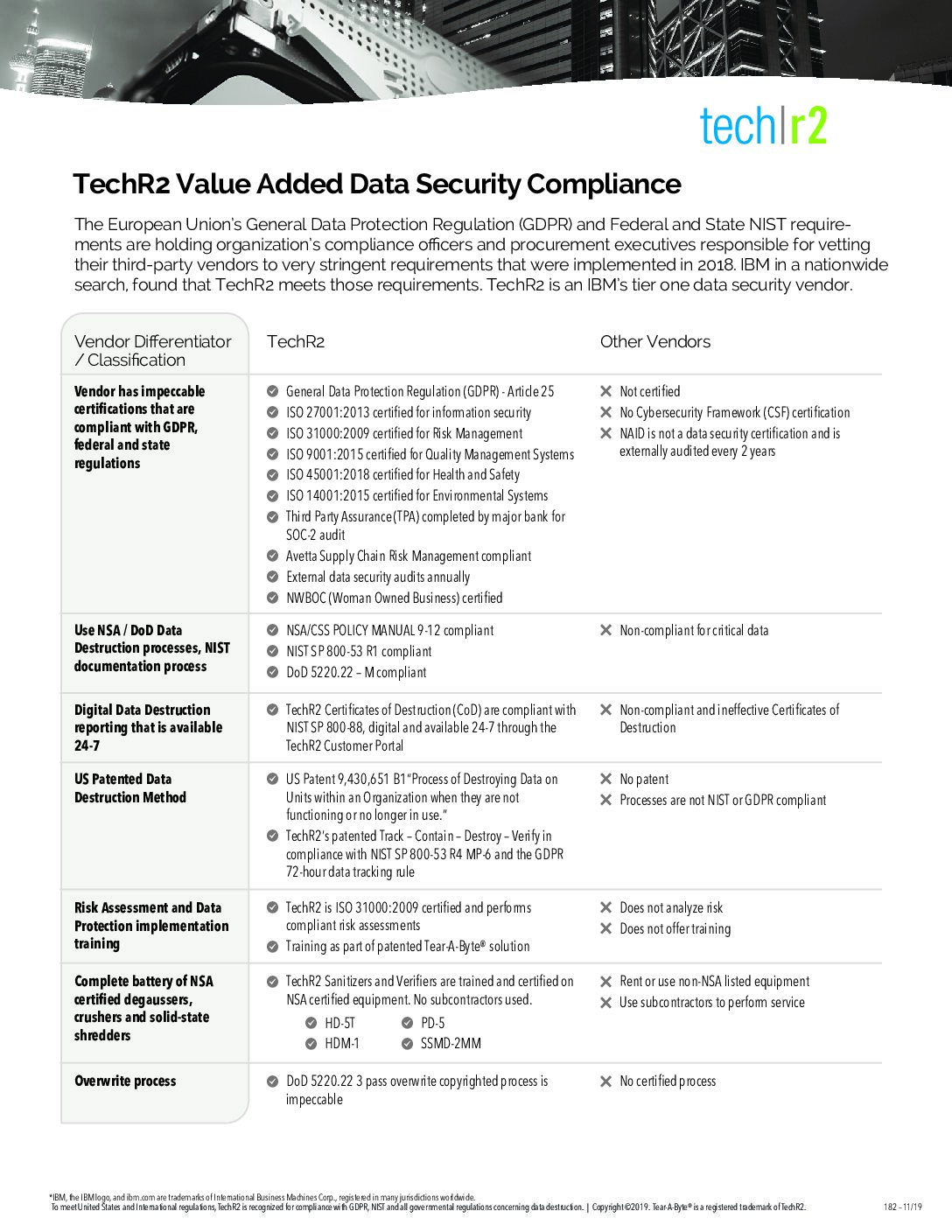
| 182 TechR2 | Vendor Differentiator Classification | 2 MB | white-papers | |||
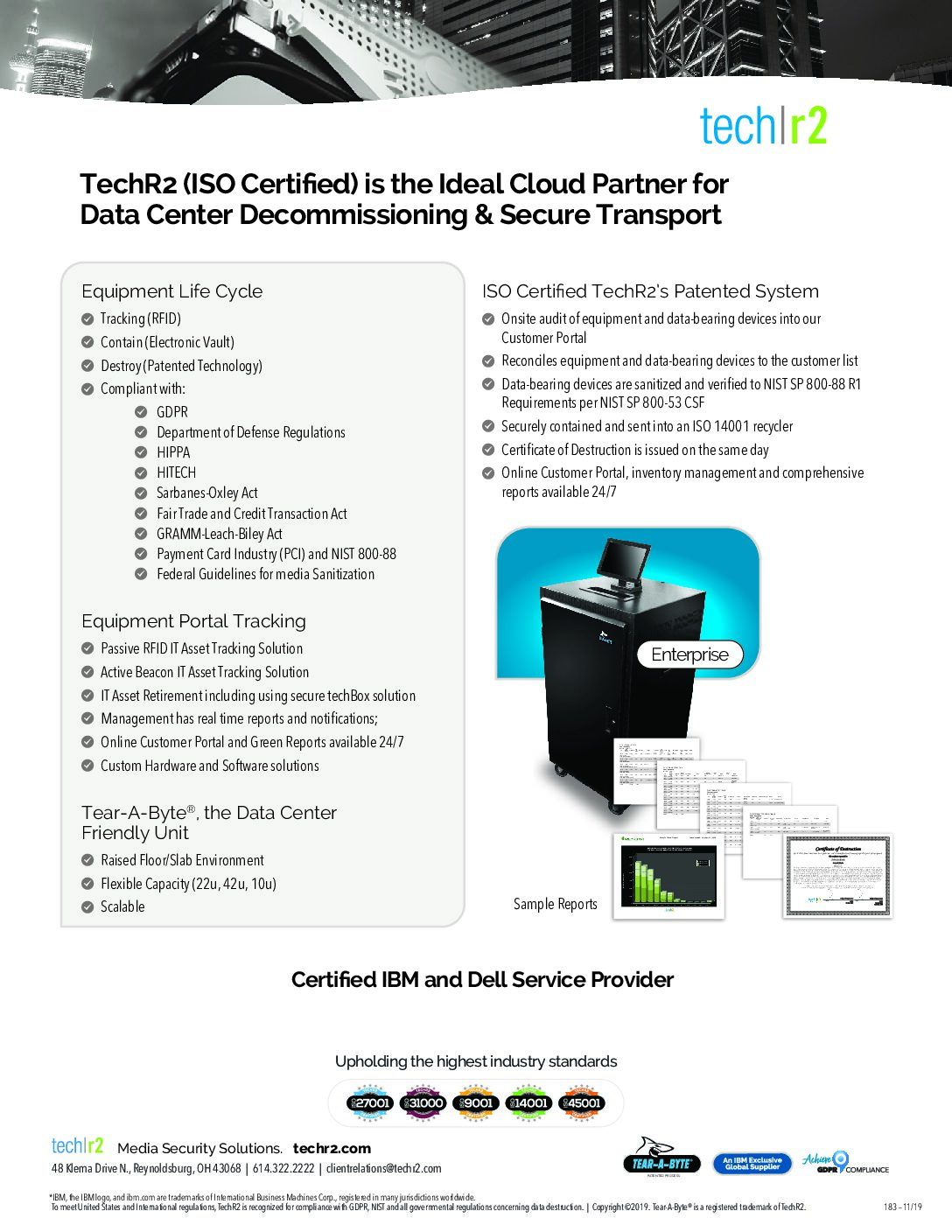
| 183 TechR2 | Cloud Partner | 3 MB | white-papers | |||
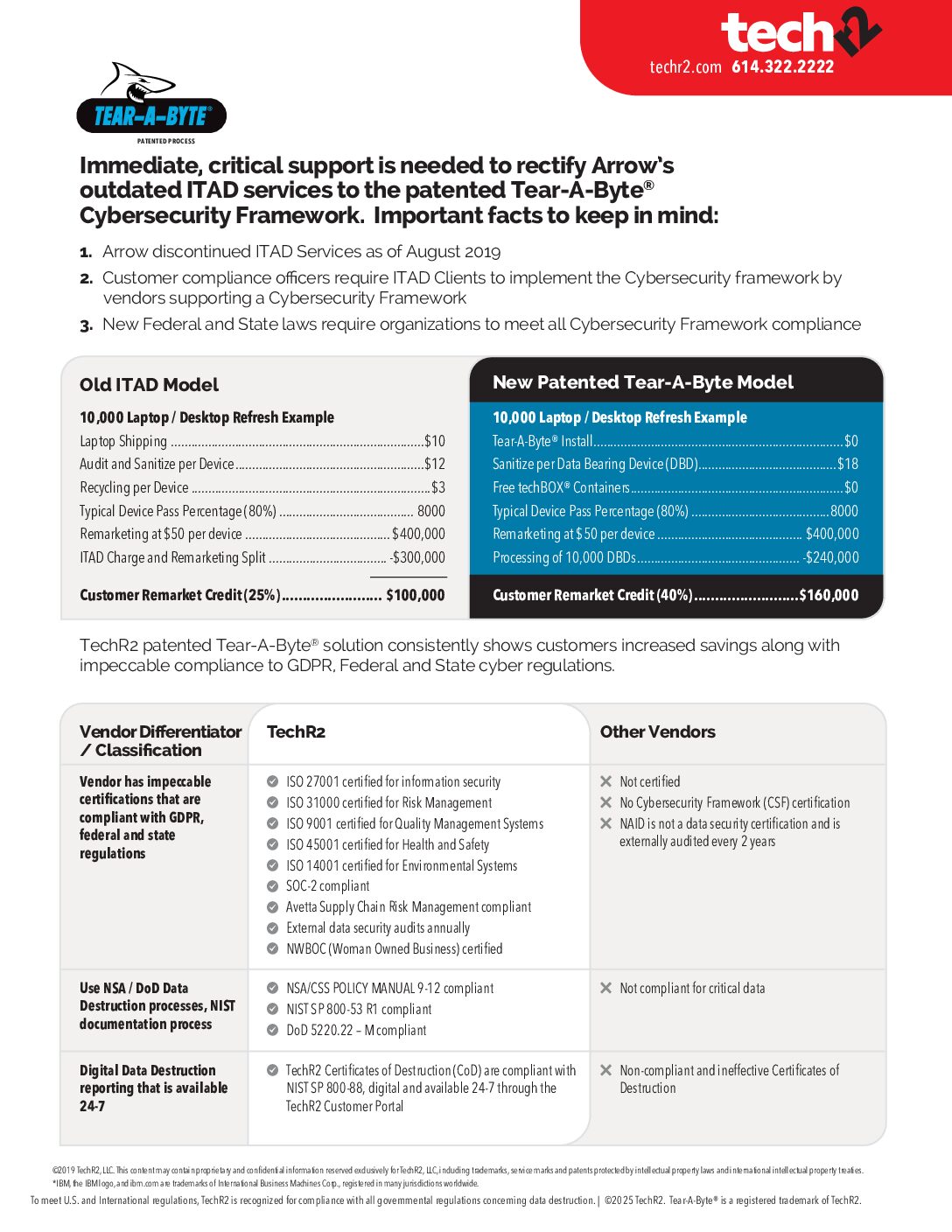
| 184 TechR2 | Tear A Byte® vs Old ITAD Model | 189 KB | brochures white-papers | |||
| 201 TechR2 | DDaas | 9 MB | white-papers | |||
| 202 TechR2 | The Road To Compliance | 5 MB | brochures | |||
| 208 TechR2 | What happens to your data assets when they reach end of life | 3 MB | white-papers | |||
| 209 TechR2 | Meeting Government Regulations | 2 MB | white-papers | |||
| 223 TechR2 | Tear A Vault | 19 MB | brochures | |||
| 224 TechR2 | Carbon Footprint | 4 MB | white-papers | |||
| 225 TechR2 | SMART TechBOX | 5 MB | white-papers | |||
| 226 TechR2 | Securing EOL | 10 MB | white-papers | |||
| 227 TechR2 | Securing DDaaS Transport | 10 MB | white-papers | |||
| 228 TechR2 | Capabilities | 1 MB | brochures | |||
| 229 TechR2 | DDaaS Capabilities | 3 MB | brochures white-papers | |||
| 230 TechR2 | Probabilities | 492 KB | brochures | |||
| 233 TechR2 | What Clients Say | 1 MB | brochures | |||
| 234 TechR2 | Case Studies | 1 MB | brochures white-papers | |||
| 235 TechR2 | DDaaS vs Per Piece | 1 MB | brochures white-papers | |||
| TechR2 | 2022 Industry Weaknesses | 137 KB | white-papers | |||
| TechR2 | GROW Licking County Release | 212 KB | white-papers | |||
| TechR2 | Pioneering Data Eradication | 360 KB | white-papers | |||
| TechR2 | Safety Triad Guidelines | 917 KB | white-papers |