Beyond Compliant
Most end-of-life IT solutions are compliant-ish.
Our patented processes and compliance-obsessed team will ensure you get and stay completely compliant.
But being compliant is just a baseline.
Our job is total data eradication.

It Comes Down to Being Responsible
Responsibly handling retired data-bearing devices is key to protecting…
- Customer information
- Intellectual property
- Your brand’s reputation
- Your company’s bottom line
- The environment
How Serious Is This?
The number one cause of large-scale data breaches is data-bearing devices ending up in the hands of the wrong people.
From hard drives and laptops, to smart phones and point-of-sale units, data-bearing devices can give bad guys more than just the data on that device. The information on those devices can also give someone the info they need to infiltrate your entire system.
Always Compliant
Multiple US, EU, and other organizations have developed and enforce data-security and environmental regulations regarding retired drives and IT devices.
It’s our job to track these regulations and ensure that our policies meet or exceed them… so our clients don’t need to worry about it.
TechR2 policies and processes meet or exceed all current and proposed USA regulations, and we’re fully compliant with GDPR – the strictest EU regulations regarding data security.
And by TechR2 being compliant, we offer our clients “safe harbor,” meaning they’re insulated from financial penalties associated with data breaches.
The Most Compliant Solution
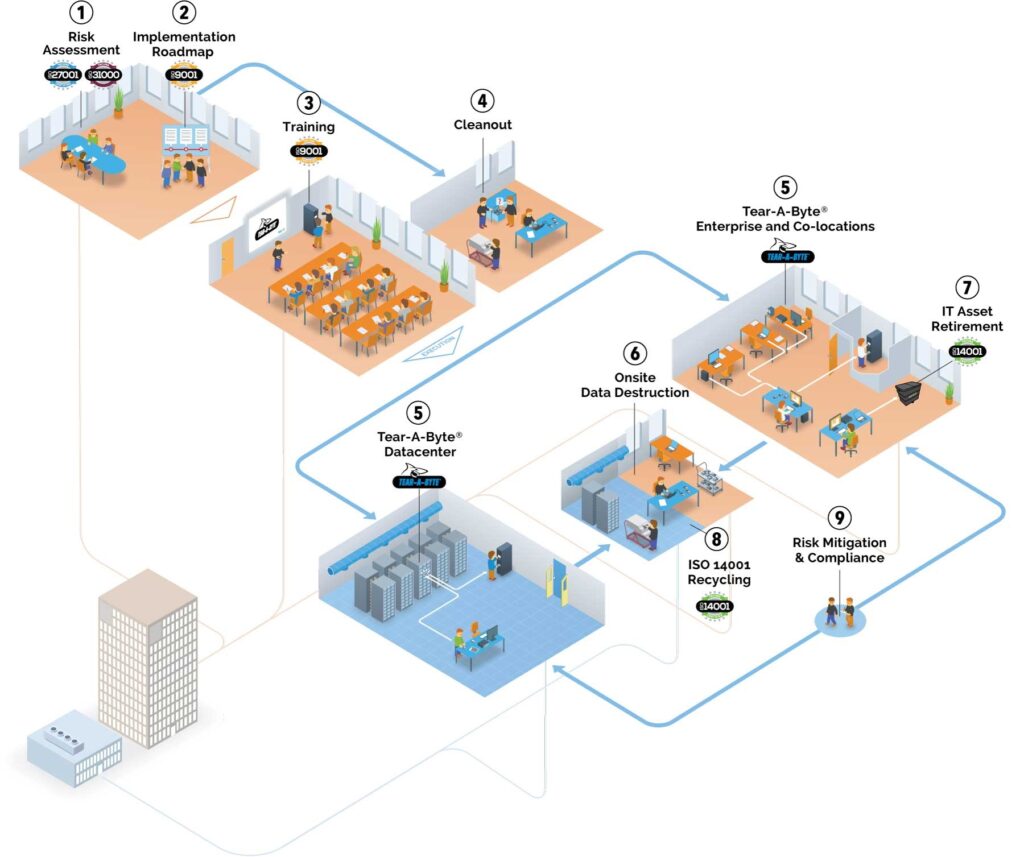
Our patented Tear-A-Byte appliance and process ensure your compliance and protect you from data breaches related to mismanaged failed or retired drives in your datacenter.
According to both leading consultants and federal and international regulatory bodies, the only way to ensure the sensitive data on your failed drives is secure is to allow no drives to leave your facility until all data is thoroughly eradicated, and you have Certificates of Destruction to prove that eradication.
Tear-A-Byte is the only solution that can provide this level of security, confidence, and compliance.

